The task was simple: two computers (notebooks). One - we call it A - with a working operating system (Xubuntu) and a new one - we call it B - without operating system. This is how I proceeded:
- Create bootable flash drive with in my case Arch-Linux
- In the Arch-Linux boot loader, press [TAB] and add "copytoram" to the boot command to load the squashfs image into ram. I needed this because in this case I only had a flash drive at hand. If you have two, you don't need this.

- List network devices:
ip address
- Assign a IP adress to computer A with:
ip address add <machine A ip adress> dev <ethernet device>
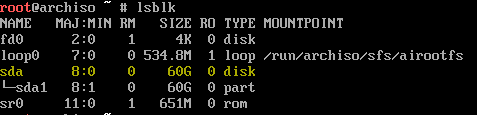
- To identify source disk, list all block devices with:
lslbk
- Prepare the copy operation (do not execute yet!) with
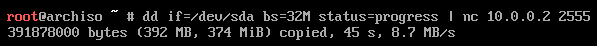
dd if=/dev/<source block device> bs=32M status=progress | nc <machine B ip adress> <random port number>
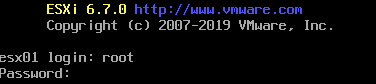
- Boot machine B from the same or different flash drive
- Assign different IP adress
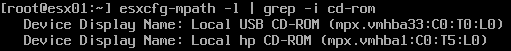
- Identify target device
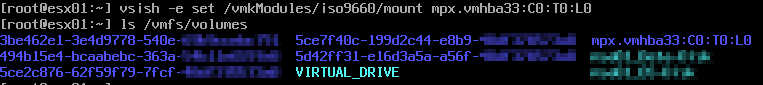
- Prepare the receiving copy operation with
nc -l -p <same port number as A> | dd of=/dev/<destination block device> bs=32M status=progress
- Execute the command on Machine B

- Then execute the command on Machine A
- Wait until the copying process is completed.
- Use at least the Sync command to synchronize corresponding file data in volatile storage and permanent storage
- Restart the machine, you are done
How it works/remarks
dd reads the source drive bit by bit into the normal output stream. The output stream is piped to netcat, which sends it over the network to a receiving netcat process (server with -l). Therefore the server must be started first. The server receives the bits and piped them back to dd, which writes them to the target on machine B.
Maybe this is not the best and/or most efficient way, but transfer speed in my case of 75MB/s (poor performance on screenshots is from a setup with two vm's) is in IHMO very good for this simple setup.
Thanks to pmenke for his support.